Insider threat ‘Insider threat’ is the term used to describe a malicious threat to a business or organization from someone who has inside knowledge. It’s one of the biggest cyber security threats that businesses face. An insider threat most often …
There are several factors to consider in the process of establishing, scaling and maintaining a modern business in today’s fast-paced corporate ecosystem. While the list of factors to consider in building a successful business are numerous, there is no doubt …
Endpoints are the communication entry and exit point of an organisation’s network. Laptops, desktops, servers, mobile phones, tablets, and virtual environments can all be considered endpoints. These endpoints usually help in accomplishing daily business tasks like sending and receiving emails, …
People used to claim they had nothing to hide when surveillance programs were implemented with cameras and border checks but now that’s no longer true. In the past few years’ rules have been modified in many countries such as American …
Over the years, Apple devices have proven to be more secure than their Windows and Android cousins, as a PC user of many years, I vividly remember the cloak of invincibility that Apple users bragged about. They looked down on …
Customized Systems Development Dynamic Planner for Investments and Pensions Planning System Integration with Payment Gateways Port Billing Operation System Hospital Management System Casual Labor Management System Customer Relations Management System Human Resource Management System Speak to our experts to get …
We are thrilled and excited to announce the launch of our newly designed website. Visit us at www.citsys.com. After several months of hard work and dedication, we are delighted to officially announce the launch of our new website. Our CEO …
With over 120 branches across Ghana, this leading financial institution serves a diverse customer base both – business to business (B2B) and business to customers (B2C) market segment. Banks and Financial institutions have long been a major target for cybercriminals …
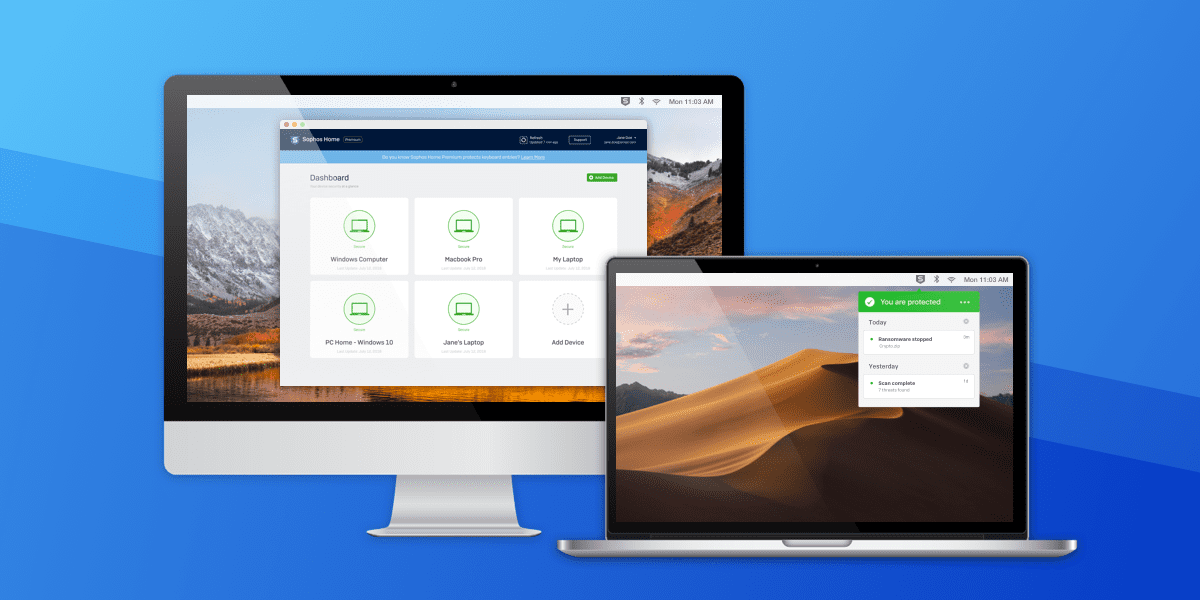
Internet Security software is essential to keep your devices safe from internet predators as well as protecting your identity, money, reputation and network infrastructure. The best antivirus software’s combine watertight virus protection, extra features to keep you safe from scams, …
Reliable protection without slowdowns Objectively deliver professional value with diverse web-readiness. Collaboratively transition wireless customer service without goal-oriented catalysts for change. Collaboratively. Progressively disseminate sustainable “outside the box” thinking before end-to-end ideas. Dramatically disintermediate resource maximizing action.